
Ransomware Insurance for Companies USA: Protect Your Business

One Friday afternoon, a small clinic woke to locked systems and a ransom note. The owner felt panic, but a quick call to their carrier brought a negotiator and a plan. That help cut costs and got critical systems back online.
This guide shows why cyber insurance is no longer optional for your business. Attacks now pair encryption with data theft, and average incident costs top millions.
You’ll learn what coverage to expect, how policies speed recovery with negotiators and forensics, and how liability insurance fits into your overall risk plan. We also give clear, practical advice so you can compare policies and avoid costly gaps.
SMBs often pay modest premiums, but what matters most is the help you get when seconds count. Use our tips and a trusted resource on business liability options to request quotes that match your true risk.
- Why ransomware insurance matters in the United States right now
- What ransomware insurance is and how it fits into cyber liability
- Core coverage you should expect in a ransomware policy
- What’s commonly excluded (and where separate endorsements apply)
- Ransomware insurance for companies USA
- How much ransomware insurance costs in the U.S.
- Underwriting requirements you’ll likely need to meet
- Industry-specific risks and coverage considerations
- How to compare U.S. carriers and policy options
- Choosing limits, deductibles, and useful endorsements
- From incident to claim: what happens when you’re hit
- Your next steps to secure coverage and strengthen resilience
Why ransomware insurance matters in the United States right now
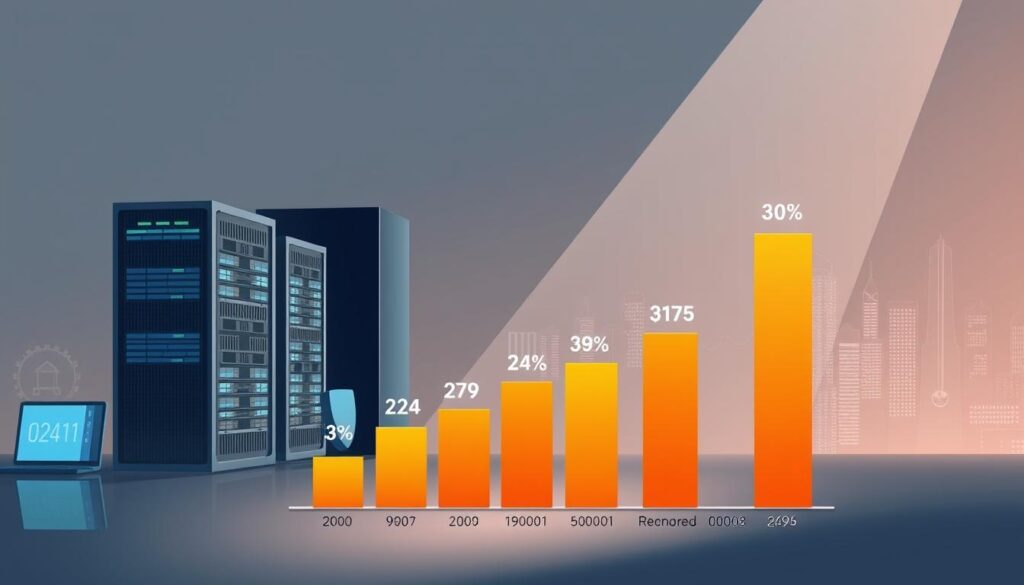
Today, attacks often steal data before they lock systems, changing the risk you face. In 2024, 94% of incidents included exfiltration and the average total cost hit $4.88 million.
Present-day risk: rising attacks, data exfiltration, and soaring claim costs
Data theft now accompanies many breaches, raising legal duties and PR exposure. Even a single data breach can trigger notification obligations, credit monitoring needs, and heavy recovery costs.
Commercial stakes: downtime, lost revenue, and reputational harm
When systems go offline, lost sales, contract penalties, and customer churn follow fast. For many businesses, the choice is pay, rebuild, or restore from backups and that choice comes with steep costs.
- Market tightening: carriers raise rates, add exclusions, and demand MFA, patching, encryption, and training to qualify.
- Business continuity: coverage can fund interruption, forensics, and legal help so you recover faster.
What ransomware insurance is and how it fits into cyber liability
An effective cyber policy blends financial protection with hands-on incident support. That mix usually lives under a broader cyber liability package that covers extortion response, restoration, incident response, and business interruption.
First-party vs. third-party protections
- First-party coverage pays for your immediate losses: forensics, system recovery, notification, crisis PR, and business recovery costs. It can also fund negotiators who work to limit payouts.
- Third-party protection defends against claims made by customers, partners, or regulators when your data or sensitive information is exposed. This is where liability insurance overlaps with privacy and legal defense costs.
- Ask about sublimits, waiting periods, and triggers before you bind a policy.
- Map how your company handles PII, PHI, and financial records to shape limits and endorsements.
- Use breach coaches and retained response teams to reduce errors and speed claims.
Core coverage you should expect in a ransomware policy
A solid policy covers more than a payment it brings negotiators, tech teams, and funding to get you back online.
Ransom and cyber extortion support: Expect expert negotiators who assess threats, work with counsel, and aim to lower ransom demands. Policies often coordinate with law enforcement and specialized vendors to manage the situation.
Business interruption and dependent vendor downtime
Business interruption coverage pays lost income and reasonable extra expenses while your systems are down. Confirm whether dependent vendor outages are included so supply-chain stoppages don’t leave gaps.
Forensics, recovery, notification, and credit monitoring
Coverage should fund digital forensics to find the attack vector and show what data an attacker accessed. It also pays to restore servers and endpoints so you can resume operations fast.
Policies commonly include legal guidance for state-required notification, plus credit or fraud monitoring for affected customers.
PR and crisis communications to protect your brand
PR and crisis services help manage media, craft customer messaging, and limit reputational harm. These services reduce long-term expenses tied to lost trust.
- Verify waiting periods, sublimits, and pre-approval limits.
- Confirm coverage spans initial compromise through exfiltration and later extortion attempts.
- Document vendor outages to support dependent-network claims.
| Coverage Area | Typical Inclusions | Why it matters | Questions to Ask |
|---|---|---|---|
| Ransom & Extortion | Negotiators, payment funds, legal coord. | Can reduce payout and speed resolution. | Are negotiators on retainer? Law enforcement coordination? |
| Business Interruption | Lost income, extra expenses, vendor losses | Offsets revenue loss during downtime. | Are dependent vendors covered? What is the waiting period? |
| Forensics & Recovery | Investigation, restoration, malware removal | Identifies root cause and restores systems. | Which vendors do you use? Are restoration costs capped? |
| Notification & PR | Legal notices, credit monitoring, PR firm | Protects customers and reputation post-breach. | Does the policy fund state-required notifications and monitoring? |
What’s commonly excluded (and where separate endorsements apply)
Not every loss is covered; many common scenarios sit outside standard policy language. Read exclusions early so you can plan to absorb or transfer those risks.
Regulatory fines, cyberwarfare, and physical property
Regulatory fines and penalties are often excluded. Claims tied to sanctioned acts or state-directed attacks tend to fall under cyberwarfare exclusions.
Physical property damage, like destroyed servers, usually needs a specific endorsement to be paid. Don’t assume hardware replacement is automatic.
Accidental damage, natural disasters, and EDP riders
Accidental damage and natural disasters commonly sit outside basic coverage. An Electronic Data Processing (EDP) rider or separate policy may close that gap.
"Carriers may deny claims if basic controls like MFA, patching, and training are missing."
Some carriers limit or exclude ransom payments, and they review your baseline security when a loss happens. Keep clear documentation of controls and pre-approval steps to protect coverage and limit unexpected costs and liability.
Ransomware insurance for companies USA
Carriers present a range of options — from fast online quotes to agent-driven programs with retained experts. You’ll see packaged plans that suit different industries and business sizes.
Match services to your risk. Healthcare, education, retail, and tech have different data mixes and regulatory duties. Pick coverage that prioritizes ransom handling, interruption, forensics, and customer notification.
- Speed vs. depth: instant quotes work for low-risk profiles; bespoke programs give deeper support for high-exposure firms.
- Value-adds: breach coaches, PR teams, and dependent network coverage reduce downtime and reputational loss.
- Contract details: compare sublimits, waiting periods, and endorsements that change payout and services.
When you request quotes, supply clear information: record counts, endpoint totals, vendor dependencies, and controls in place. That reduces surprises in underwriting and speeds approvals.
Want a quick starting point? Review options and get comparative quotes and program details to see how carriers stack up against peers in your industry.
How much ransomware insurance costs in the U.S.
Expect to pay a modest monthly premium, but the real cost depends on how exposed your systems and data are.
Median pricing: Insureon reports the median cyber premium for small businesses is about $145 per month. That gives a starting benchmark when you shop.
Several clear drivers move costs up or down. The number of endpoints, data volume and sensitivity, and annual turnover are top inputs.
- Industry risk: healthcare, education, and government made up 47% of attacks in 2024, raising premiums in those fields.
- Limits & deductibles: higher limits raise premiums; larger deductibles lower them.
- Controls & history: MFA, backups, and EDR reduce premiums. Prior claims push prices higher.
What the policy typically covers and budgeting tips
Coverage often pays for forensics, recovery, business interruption, and legal costs tied to an attack. Plan for both premium payments and out-of-pocket deductibles.
"Right-size limits and compare apples-to-apples. A low sticker price can hide sublimits and gaps."
Underwriting requirements you’ll likely need to meet
Underwriters focus on practical controls that prove you manage cyber risk every day. You’ll need to show clear evidence that critical systems use multifactor authentication, regular patching schedules, encryption, and modern endpoint protection.
MFA, patching, backups, and endpoint protections
Carriers expect reliable backups with offline or immutable copies and routine restore tests. They also look for network segmentation and privileged access management to limit lateral movement.
Employee training and documented incident response plans
Documented policies and an incident response plan that you test regularly improve your terms. User training that reduces phishing and credential theft lowers your loss profile and speeds claim handling.
- What to prepare: screenshots, logs, patch records, and written policies.
- Prioritize: MFA first, then backups, then endpoint agents and segmentation.
- Watch warranties: some policies require you to keep controls in place or face denial of coverage.
Industry-specific risks and coverage considerations

Industry role and data exposure drive what protections matter most when a breach happens. Different sectors face distinct loss patterns and policy needs. That makes shopping by sector essential.
Healthcare, education, government, and financial services
Healthcare, education, and government made up nearly half of high-impact incidents in 2024. That raises premiums and pushes carriers to require strict controls.
Financial services must prioritize liability protections and fast reporting. Regulators expect clear remediation plans and tight record-keeping.
Retail, real estate, and tech with third-party exposure
Retail and real estate handle large volumes of PII, so robust notification and credit monitoring matter most to limit customer harm.
Tech businesses often need both first-party recovery and third-party liability because client contracts shift responsibility for client environments and data.
- Contract clauses can force minimum limits, quick response timelines, and specific endorsements.
- Sublimits and waiting periods often determine whether you can meet uptime and transaction needs.
- Show underwriters your controls and testing to lower premiums and improve terms.
"Match coverage to how you actually operate map data types to policy elements and test your response plan."
For recent industry trends and carrier expectations, review carrier guidance and renew with documented improvements to reduce liability and cost.
How to compare U.S. carriers and policy options
Start by listing what each carrier actually does — services matter more than a low price. You want a clear view of coverage, vendor panels, and how fast help arrives when an incident happens.
Evaluating Travelers, Nationwide, NEXT, and AmTrust
- Travelers pairs strong financial ratings with access to cybersecurity coaches and the eRiskHub via agents.
- Nationwide offers broad coverage options and enhancements like dependent network BI and regulatory fines add-ons plus loss prevention services.
- NEXT is best when you need instant quotes and online binding with 24/7 expert help.
- AmTrust suits small businesses seeking low entry limits (starting at $50,000) and combined first- and third-party coverage, including dependent interruptions.
Coverage breadth, limits, add-ons, and responsiveness
- Confirm extortion response, forensics, restoration, dependent network BI, and sublimits for key areas.
- Evaluate included services breach coaches, PR, legal guidance and activation speed during breaches.
- Assess quotes by total value: waiting periods, panel vendors, reporting rules, and claims handling matter more than sticker cost.
- Verify how each company documents dependent network losses and whether regulatory fines need an add-on.
Choosing limits, deductibles, and useful endorsements
Treat limit-setting like budgeting a recovery plan: list assets, vendors, and likely downtime. Start by mapping how many records you hold, annual revenue, and critical systems that would stop under an outage.
Right-sizing limits based on records and revenue
Small firms that handle a few thousand PII records often target around $1 million limits as a baseline. AmTrust offers entry-level limits near $50,000 if you need starter protection.
Match limits to contractual duties and potential regulatory exposure. Higher liability limits matter when client contracts or state rules push recovery costs into six figures.
Business interruption, dependent network, and asset restoration
Buy business interruption limits that reflect realistic downtime. Use recovery time objectives (RTOs) to estimate lost income and extra expenses.
Add dependent network and asset restoration endorsements when key vendors or cloud platforms could cause extended outages. Nationwide’s enhancements include dependent network BI and regulatory fine options to fill these gaps.
- Check deductibles and waiting periods: lower premiums raise out-of-pocket risk when an event occurs.
- Layering and sublimits: ensure sublimits don’t undercut core coverage in high-cost areas like forensics or PR.
- Review annually: update limits as your data, revenue, and infrastructure grow so the policy keeps pace.
From incident to claim: what happens when you’re hit
When systems go dark, your first minutes shape the rest of the recovery. Act quickly: isolate affected systems, preserve logs, and contact your broker or carrier without delay. They will activate breach coaches, panel forensics, and legal counsel to guide the next steps.
Immediate steps, carrier coordination, and legal requirements
First 24 hours checklist:
- Isolate affected systems and preserve evidence.
- Contact your carrier and activate approved response vendors.
- Engage legal and PR resources to meet state notification rules.
- Track all expenses and labor tied to recovery.
Carriers often supply negotiators to manage ransom discussions and review payment approvals. Coordinate with forensics to validate scope, restore clean backups, and prevent reinfection before returning systems to production.
Avoiding claim denials: negligence, insider threats, and known flaws
Document everything: alerts, timelines, patch records, and configuration snapshots. Claims can be denied if MFA, endpoint protection, or timely patching are missing.
"Keep clear evidence of controls and action—underwriters look for proof as soon as a claim is filed."
| Action | Who | Why it matters | What to save |
|---|---|---|---|
| Contain & preserve | IT / Forensics | Protects evidence and limits further damage | Logs, memory images, snapshots |
| Notify carrier | Broker / Company Exec | Triggers panel vendors and legal support | Incident summary, contact list |
| Communicate externally | PR / Legal | Meets state breach notice and limits reputational harm | Drafts, timelines, customer lists |
Your next steps to secure coverage and strengthen resilience
Begin with a clear map of your data, systems, and vendor links so you see where downtime would hurt most.
Inventory critical assets, gather proof of controls like MFA, backups, and EDR, and keep your incident plan ready. These steps help small businesses secure more favorable quotes from NEXT, Insureon, and agent-led programs such as Travelers, Nationwide, and AmTrust.
Request quotes that list limits, sublimits, waiting periods, and included services. Align coverage and endorsements to real dependencies cloud platforms and key vendors to avoid surprises during an incident.
Model outage costs, build a customer communication plan, run tabletop exercises, and keep an evidence folder. Revisit your program yearly to match growth and shifting risk.






Leave a Reply